HOW TO ACHIEVE ISMS CONTINUAL IMPROVEMENT
Standard Requirement for ISMS Continual Improvement

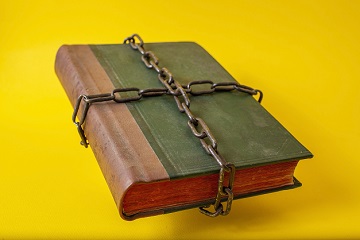
A mysterious statement at the end of the ISO 27001 standard requires that “the organization shall continually improve the suitability, adequacy and effectiveness of the information security management system.” It is a recurring question, how to deal with continual improvement? Should it be a standalone process or a cumulative outcome of other processes? One thing is certain: the standard doesn’t support sitting back and saying that our management system is ready and perfect.
Interesting Historical Background
Some 20 years ago, the BS 7799-2 British standard, the direct predecessor of the ISO ISMS standard line and the one against which I have started auditing, already contained the requirement to continually improve the management system. It provided the additional guidance that the objective had to be achieved “through the use of the information security policy, information security objectives, audit results, analysis of monitored events, corrective and preventive actions and management review.”
The requirement was transferred without modification to the first ISO standard, issued in 2005. Although the preventive action process doesn’t exist anymore, this list contains all the instruments of the current standard that are used to improve something by planning and implementing it. The omission of this guidance from the current issue does not imply a change in the approach of the standard; it only fits into the general process seen in the recent ISO standard issues, that standard-writers give more freedom to the users in how to implement the requirements.
And this is not the only improvement-related simplification: until the 2005 issue of the standard there was a chapter in the standard that emphasized process approach. Until then, reference to the Plan-Do-Check-Act (PDCA) cycle was an integral part of the standard. This meant that every process operated as part of the management system has to be planned, implemented, monitored, and improved. This was an ever-repeated cycle and still is today. This approach is still inherent in the standard, without explicitly referring to the PDCA cycle.
How to Efficiently Improve the ISMS?

Taking a look at the earlier information security standards showed that continual improvement is a result of several processes of the ISMS. An unlisted but compulsory tool of continual improvement is risk management. If you operate those processes, you are doing continual improvement. You are encouraged, however, to introduce any other processes you find suitable for your organization. A trivial option is to plan and implement changes based on input from interested parties.
There are also control-level tools to improve the ISMS coming from Annex A of the standard, like regular review of policies and information security continuity controls, learning from information security incidents.
Efficiency is not a standard requirement (the standard refers only to effectiveness) but a strong business need. Continual improvement doesn’t necessarily mean lower risks but achieving the same risk level more efficiently.
How to Easily Document and Monitor Improvement Actions?

As we have seen, there are many channels for improving information security. This means that you need to monitor many actions. You can reduce the burden by contracting a few sources of action plans.
Nonconformities may come from many sources, but if you consider third-party or internal audit as one of them, you can document and follow up audit findings as nonconformities.
There are several action plans that typically cover longer terms and are more general. Documenting actions to achieve ISMS objectives, risk treatment plans, and management review decisions in a single development plan may also be feasible.
